Policy Management as a Service
Setting The Standard In IT Policy Excellence
The first step towards creating a secure computing environment is to develop IT policies and procedures that document the management and control of digital information.
To be successful, information systems security policies must be written using easy to understand language so that all parties understand the requirements and their obligations associated with the use of company information.


Five Common Challenges
- No one in-house has the subject matter expertise or experience in writing IT Policies
- Existing policies are seldom reviewed to keep them up to date with changes in business and technology usage requirements
- Writing and maintaining policy content in-house or on a bespoke basis is laborious and expensive
- Stakeholder and user engagement requires a lot of management and effort
- Monitoring and measuring user engagement with the content is difficult
Policy Management as a Service
Protocol Policy Systems have developed a generic set of IT security policies, which are then uniquely tailored to align with your organisation’s practices.
Policy Management as a Service is a cloud-based subscription solution available in 3 versions – Lite, Essentials and Premium. The service allows an organisation to deliver up to date IT policies in under 5 weeks, eliminating the overhead of creating and maintaining those policies in-house.
All the hard work of gaining expert knowledge, developing, and maintaining policies to keep them current and mapped to standards such as ISO, PCI-DSS, and the ASD Essential Eight is taken care of by our experts on behalf of our customers.
Once in place, the policy management software makes the process of engaging and monitoring stakeholder and user interaction with the content both easy and visible.


What Does Policy Management as a Service Do?
- Helps protect the assets of a business
- Provides an organisation’s IT security framework
- Provides a uniform level of control and guidelines for management
- Communicates security messages and training in a format that is easily available and understood
- Advises team members about their responsibilities to the policies
- Endorses the commitment of the CEO and senior management to protect valuable information assets and improve security posture
How The Policies Are Organised
Policy Management as a Service includes 25 comprehensive policies covering key aspects of information system usage. All policies are written in plain English, with drop down explanations and links to relevant standards. The policies are set out by category for User, Manager, or Technical team members, which allows easy access to the policies that specifically relate to them.
The service also supports additional governance policy content, customers manage these documents in their unique instance of PMaaS and make use of many of its features and functions.


Compliance With Standards
Organisations adopt standards to help them optimise their business operations, manage risk, or comply with regulatory requirements. As an example, ISO 27002 is the code of practice for information security in many countries including Australia, New Zealand and the U.K. It sets the criteria for achieving best practice security management. Because all of the policy statements in Policy Management as a Service are mapped to international standards and best practice guidance, it provides evidence that security is being taken seriously by management, and stakeholders can have confidence that the organisation is acting responsibly.
User Engagement
Policy Management as a Service has been designed to address many of the shortcomings of in-house bespoke policy initiatives which may not address stakeholder and user engagement considerations. Examples of options the service provides include:
- SAML integration with Azure AD or ADFS for single sign on
- Stakeholder input regarding policy wording in the system throughout the initial delivery phase
- Present enrolled users with specific content from the overall policy framework to review
- Invite third parties that are required to work with your systems and data to create a login and view the policy content
- Review and accept policies onscreen – time efficient with no paperwork required
- Create quizzes based on your custom Acceptable Use Policy to test user comprehension
- Generate user interaction reports
- Get further detailed visibility through Insite Compliance reporting
- Help users to develop and improve their understanding of the need for good security behaviours with our security awareness videos, topic index, glossary of terms and Top Tips page


Keeping Up To Date
Under the Policy Management as a Service subscription plan all policy content is automatically kept up to date by us, as are the standards, mappings, and supporting material. Our subject matter experts are also available to adapt policies for customers as their business requirements change.
Click here to read our case studies.
Click here to read testimonials from our customers.
Demonstration Videos
IT Policy Challenges
This video highlights the common challenges of developing, delivering, and maintaining IT Policies.
PMaaS In-depth
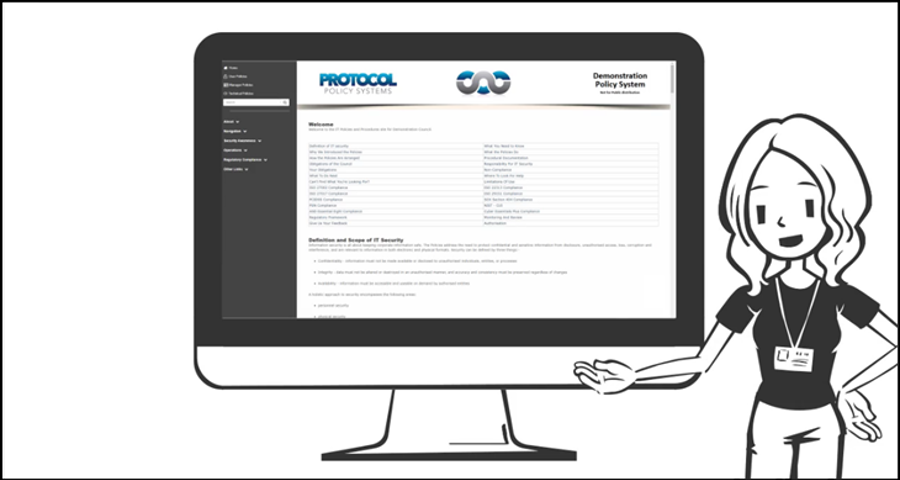
This video steps through the key aspects of the Policy Management as a Service offering.