


02 December 2020
Wrapping up 2020
This is our last newsletter for 2020 so we would like to wish our readers all the best for the pending holiday season. The team at Kaon Security are looking forward to a well-earned break however, we will be available between the statutory holiday dates for any requests or emergencies.
Procurement Panels
Kaon Security are very pleased to advise that we are now listed as a security consulting services provider on the Local Buy government procurement panel for Queensland and the NZ Government focussed Marketplace. The full range of our services is now listed on the respective websites of these two procurement bodies.
Microsoft 365 Security Audit Service Enhanced
We recently updated and streamlined our Microsoft 365 Security Audit, which is designed to help organisations ensure their 365 environment is secured correctly. There are 5 key elements to this service -
- Assess the current configuration and the available supporting customer information
- Conduct a risk analysis of the Microsoft 365 implementation
- Make recommendations to improve the organisational security posture
- Document remediation points
- Deliver a comprehensive report on the above
Reporting Updated
Kaon Security provides your organisation with a detailed, comprehensive report which includes:
- Executive Summary of the Microsoft 365 Security Audit which is specifically written for business people.
- Detailed Key Observations and Recommendations covering our findings, risk analysis commentary, and recommendations for security posture improvement.
- Configuration review analysis classifying all identified issues; noting their current and recommended optimal security settings; risk severity rating; remediation time and complexity grading; security impact rating.
- Issue classification breakdown by type e.g. – misconfiguration, data security etc.
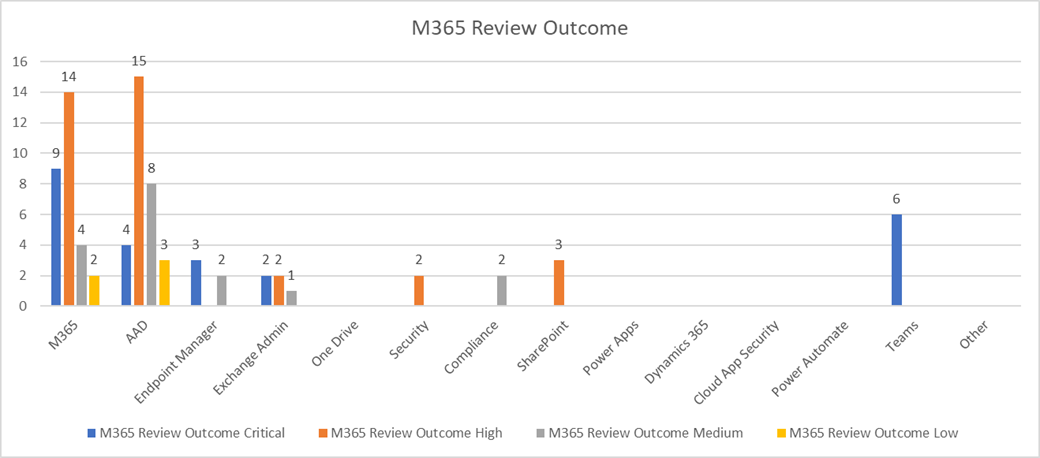
The information is presented in an easy to read format and includes a selection of new charts:
And there’s more... in addition to this report, Kaon Security supplies a separate folder of supporting information which includes media files of the areas identified as requiring review and remediation.
Contact Mike or Steve to discuss the enhanced service and to get a quote.
IT Third Party Risk Management
How do you ensure that third parties engaged to do work for your organisation preserve the confidentiality, integrity, and availability of your information? – NB, the “work” could include access to your organisation's data, intellectual property, financials, operations, or other sensitive information.
Some questions to consider are -
- Do you have an accurate inventory of all the third parties that you rely upon?
- Can you identify which third parties are critical to your business?
- Can you identify which third parties pose the highest risk to your organisation?
- Do you know which third parties have access to your data?
- Do you have a signed contract with third parties that allows you to enforce your organisation’s security requirements or conduct security assurance checks?
- What onboarding and offboarding process are currently documented and applied?
- How do you ensure that IT third party risk is an integral part of your risk framework?
When asked, these types of questions often elicit a blank look, or a “No” response.
We all have a reliance on third parties to make things happen so it’s important to ensure the risks associated with engaging them are analysed, understood and managed appropriately. To discuss how we can help your organisation to assess and improve its IT Third Party Risk Management give us a call.
