


24 June 2021
Brand new Policy Management as a Service solution announced
Kaon Security is pleased to announce the June 30th release of its new generation Policy Management as a Service (PMaaS) solution.
PMaaS is an enhanced cloud based policy solution that has been developed to assist organisations create, deliver, and maintain a comprehensive suite of IT policies. This new service streamlines the engagement between the users and the content, whilst providing a rich source of foundational guidance on how they should interact with organisational systems and data.
What are the highlights of the new service?
The PMaaS offering comes in three versions - Lite, Essentials, and Premium. It will be available to all new customers as of July, plus there are migration options available now for existing customers.
New Functions include* –
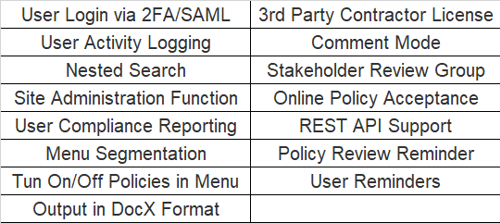
Click here to view a detailed new function matrix*
*Note: not all functions available in all versions
Ensuring the confidentiality, integrity, and availability of information
A cybersecurity strategy is a key component in guiding an organisation to take the right steps to ensure the confidentiality, integrity, and availability of their information.
The strategy document should provide an overview for senior management to assist them in making decisions about how resources should be allocated to protect their organisation’s information systems and data; ensure services they provide are secure; and underpin existing and future digital initiatives to ensure their success.
In our customer engagements we discuss a number of elements to help them develop the cybersecurity strategy including - strategy goals, scope definition, identifying stakeholders, implementation of the strategy.
If you are required to develop a cybersecurity strategy and would like objective third party input or assistance to help complete this exercise then feel free to contact us to discuss.
Preparing for recovery
Ransomware attacks continue to be a major issue for organisations and are having some devastating effects across a range of sectors recently including healthcare, food processing, and energy. With whole computer systems unavailable for use and in many cases data potentially not recoverable, the stakes are high. If recovery is possible, it may take several weeks. In the meantime your business reputation is taking a hiding, and the human cost of ransomware on your staff and customers is heavy.
The following steps will help to ensure your organisation can recover quickly.
- Identify what are your critical business assets and what would be the impact if they were attacked
- Be prepared by planning for an attack situation - even though you may think it’s not going to happen
- What is your communication strategy? - It is important that internal and external communication is timely, and sees the correct information reaching the right people that need to be kept informed
- What are your legal obligations when it comes to the reporting of incidents, and how will these obligations be addressed?
- Do you have a pre-prepared agreed response to a ransom demand, and the likelihood that the attackers will threaten to publish some of your data?
- Do you have alternative access to copies of these resources in the event that:
- You have lost system access
- You may not have easy access to key documents such as incident management playbooks, checklists, and key contacts' information
- Do you test your plan?
- If you have a ransomware attack do all the people who would be involved in working on this incident clearly understand their roles and responsibilities?
- Is everyone involved clear on the key priorities in the event of an attack?
- Review your responses! Should you experience an incident, take time afterwards to revise your incident management plan, so that you can minimise the chance of the same event occurring again in the future
Doing the work to be prepared for an incident may stretch your resources, our Incident Response Execution Pack may be worth considering to fast track your preparation. The deliverables include a workshop with one of our consultants and a selection of customised and branded playbooks.
Click here for more information on our Incident Response Optimisation service.
